-
Be sure to read this post! Beware of scammers. https://www.indianagunowners.com/threads/classifieds-new-online-payment-guidelines-rules-paypal-venmo-zelle-etc.511734/
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Half of US Hospitals Shut Down Networks Due to Ransomware
- Thread starter bwframe
- Start date
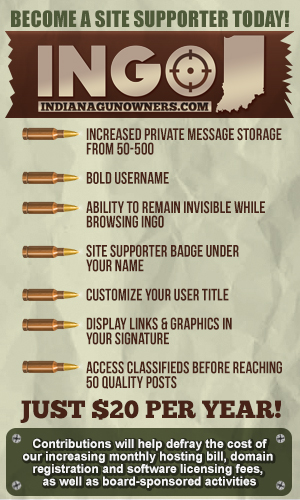
The #1 community for Gun Owners in Indiana
Member Benefits:
Fewer Ads! Discuss all aspects of firearm ownership Discuss anti-gun legislation Buy, sell, and trade in the classified section Chat with Local gun shops, ranges, trainers & other businesses Discover free outdoor shooting areas View up to date on firearm-related events Share photos & video with other members ...and so much more!
Member Benefits:
Couldnt tell by my activist RT TikToker friend. I finally had to snooze her for 30 days.The ISDH website posts the data. Hospitalizations are back to what they were in the early spring of 2020. They are half of what they were at the height of this.
What is a foolproof backup plan?That is a very funny joke!
Back to the subject though...
How is it that hospitals cannot have an IT program that includes a fool proof backup plan?
Bad guy gets into companies network. They slowly look around and gain access to more systems. They look for important data. They look for backups. They screw with the backups so they are not usable anymore. They get everything in place then drop the hammer on the company, encrypting data on as many systems as they can.
Legacy backup strategies were never designed with this kind of attack in mind. They were designed with a server crashing, data corruption, or even a large disaster in mind. These companies probably had great backup strategies for all of the old school scenarios. They just aren't as useful against this.
The victim may never find out how long the bad guys were in. They have to work through their backups to find one that is not infected, IF they have one at all. Then they have to do it again and again for each server that was infected.
_____________________________________________________
Tl/DR It is really hard to have good backups against ransomware
This **** would come to a screeching halt with some well planned, well coordinated, well executed violence.
They would comment, in return, that our well planned, well coordinated violence would come to a screeching halt with just a pinch of their **** dusted on the street in front of our metaphorical bro dozers……
And they would be correct.
I was thinking more like a JDAM in their living room. Sure there are Hellfire Missiles and Small Diameter Bombs, but I'm old-school. Before you say anything, the JDAM is almost 30 years old.They would comment, in return, that our well planned, well coordinated violence would come to a screeching halt with just a pinch of their **** dusted on the street in front of our metaphorical bro dozers……
And they would be correct.
Money. Period.That is a very funny joke!
Back to the subject though...
How is it that hospitals cannot have an IT program that includes a fool proof backup plan?
all inclusive from top to bottom
I'm retired from IT and one of the reasons that pushed me out was lack of support from management. They wanted a backup/contingency plan that covered about 9 TB of data distributed across multiple sites in the US, China and India and it has to cost less that $100,000. I'm too old for that crap.So true. You try to stop it, but you better have a good plan in place to recover if/when it does.
Last edited:
I'm so close to retiring full time I can smell it....can't wait.I'm retired for IT and one of the reasons that pushed me out was lack of support from management. They wanted a backup/contingency plan that covered about 9 TB of data distributed across multiple sites in the US, China and India and it has to cost less that $100,000. I'm too old for that ****.
Good for you buddy. I hope to join you in 2 years if I can even hold out that long...I'm so close to retiring full time I can smell it....can't wait.
Thankfully my company now realizes they have to spend money to try to protect things. I guess the headlines over the last year woke them up.I'm retired from IT and one of the reasons that pushed me out was lack of support from management. They wanted a backup/contingency plan that covered about 9 TB of data distributed across multiple sites in the US, China and India and it has to cost less that $100,000. I'm too old for that crap.
JeepHammer
SHOOTER
If you're not worried about being impacted by these kinds of attacks, you're not paying enough attention.
1's-0's from anywhere in the world from a nice, cheap computer is a much bigger threat than space launched, super expensive & complicated EMP or nuclear weapon...
-- But you can't convince the scared bunnies of that.
Water, sewage, electrical grid, natural gas & petroleum pipelines/pumping stations are front line targets, with strategic value...
The strategic planners have recommended power grids go small scale, small grid production (wind & solar) rather than big production plants since the operators of those plants & grids REFUSE to update or protect their networks.
The military has made pretty good strides in that direction, but the US commercial grid has done virtually nothing with the exception of spending money on disinformation campaigns...
It takes real scumbags to ransom a hospital...
I don't even know what a 'Proper' punishment would be.
I use that 'White List' protection, but I have no idea how good it is.
My computer expertise stops at PLC's/logic ladders.
If an actual expert has suggestions, I'm all ears...
If an actual expert has suggestions, I'm all ears...
Put evidence dangerous to hillary clinton on the systems.
Punishment? I'd say let's start at attempted murder charges for every person put on danger in the hospital.1's-0's from anywhere in the world from a nice, cheap computer is a much bigger threat than space launched, super expensive & complicated EMP or nuclear weapon...
-- But you can't convince the scared bunnies of that.
Water, sewage, electrical grid, natural gas & petroleum pipelines/pumping stations are front line targets, with strategic value...
The strategic planners have recommended power grids go small scale, small grid production (wind & solar) rather than big production plants since the operators of those plants & grids REFUSE to update or protect their networks.
The military has made pretty good strides in that direction, but the US commercial grid has done virtually nothing with the exception of spending money on disinformation campaigns...
It takes real scumbags to ransom a hospital...
I don't even know what a 'Proper' punishment would be.
I use that 'White List' protection, but I have no idea how good it is.
My computer expertise stops at PLC's/logic ladders.
If an actual expert has suggestions, I'm all ears...
PLC's in my opinion are pretty safe proves they aren't connected to the network and all firmware upgrades are thoroughly vetted.
Suggestions:
Move vital systems away from windows and use a stripped down flavor of Linux.
3-2-1 back ups. 3 copies of data, 2 on sight, one off site not in the cloud but a physical location in the states.
Back up all vital systems with redundant independent connections.
Thorough training for all persona touching any computer systems. Not that ******** watch this slide show about unknown attachments nonsense. Real applicable training in tech and social engineering.
All passwords should be at least 14 characters and change automatically on a timer, every 10 hours or so.
True multifactor access to said passwords.
Strict, access control. Only grant the lowest usable access to people.
No open shares on networks.
Lock down all ports that are not specifically needed and only open those ports on a IP basis. Lock down unneeded ports between network segments even if it's subnet to subnet on the same routing device. No layer 2 switches when it can be avoided.
All open network jacks in the building it being used, shut it off. And the ones in use only allow access to a specific Mac address on that port.
Monitor all network traffic.
Deploy a good well configured IPS/IDS on each side of the edge device(s)
Good searchable logging can not be over looked.
That's a start.
So honest question , would two factor authentication help prevent these kind of attacks? When I was at Indiana University the IT department seemed to be pretty on top of security to my untrained eyes. Every time you logged into the system you needed your usual username and passphrase , then a secondary authentication is sent to an app on your phone or a "token" to login.
I am familiar with the ways in which ransomware attacks compromise data backups (just wait for the system to back up with the Ransomeware on it) then basically controll the entire system.
Second question, since most of these attacks seem to be coming out of Eastern Europe what can we do feasibly to deter these scumbags? I mean seriously I am not a fan of the way America does healthcare but someone has to be a real piece of **** to attack a hospital like that.
I am familiar with the ways in which ransomware attacks compromise data backups (just wait for the system to back up with the Ransomeware on it) then basically controll the entire system.
Second question, since most of these attacks seem to be coming out of Eastern Europe what can we do feasibly to deter these scumbags? I mean seriously I am not a fan of the way America does healthcare but someone has to be a real piece of **** to attack a hospital like that.
No. These attacks rely on stupid people falling for stupid links. Click the link, open the attachment, etc and boom. Anything they have the ability to change gets encrypted. (or the attacker takes control and starts snooping remotely) Its more about giving users too much power/access and lack of security patches.So honest question , would two factor authentication help prevent these kind of attacks? When I was at Indiana University the IT department seemed to be pretty on top of security to my untrained eyes. Every time you logged into the system you needed your usual username and passphrase , then a secondary authentication is sent to an app on your phone or a "token" to login.
I am familiar with the ways in which ransomware attacks compromise data backups (just wait for the system to back up with the Ransomeware on it) then basically controll the entire system.
Second question, since most of these attacks seem to be coming out of Eastern Europe what can we do feasibly to deter these scumbags? I mean seriously I am not a fan of the way America does healthcare but someone has to be a real piece of **** to attack a hospital like that.
But MFA is AWESOME in general. We were getting slammed by password stealers.
User clicks the bogus link to a lookalike O365 site. They input their username and password, giving it to the bad guy.
Bad guy logs into their O365 account from Maldova and then sends a nasty virus, etc to everyone on that persons contact list (and everyone opens it because they trust the sender), as well as harvesting sensitive info from their inbox, notes, Onedrive, etc.
Now that I've turned MFA on, The worst that happens is we get a warning that BillyJoeBob failed to sign into his 365 account* from a 3rd world country while he's here in Indy. (we then change his password and remind him to pay more attention)
*Because after entering the stolen password, Billy's phone gets the authentication code to proceed, and not the hacker in that ****hole country, preventing the login attempt.
That makes a lot of sense to me, seriously thanks for taking the time to explain it.No. These attacks rely on stupid people falling for stupid links. Click the link, open the attachment, etc and boom. Anything they have the ability to change gets encrypted. (or the attacker takes control and starts snooping remotely) Its more about giving users too much power/access and lack of security patches.
But MFA is AWESOME in general. We were getting slammed by password stealer.
User clicks the bogus link to a lookalike O365 site. They input their username and password, giving it to the bad guy.
Bad guy logs into their O365 account from Maldova and then sends a nasty virus, etc to everyone on that persons contact list, as well as harvesting sensitive info from their inbox, notes, Onedrive, etc.
Now that turned that on, The worst that happens is we get a warning that BillyJoeBob failed to sign into his 365 account from a 3rd world country while he's here in Indy. (we then change his password and remind him to pay more attention)
Any time. I HIGHLY Recommend MFA (2FA) for any account that supports it. It used to be that only rich folk or enterprises that could afford expensive RSA key fob systems could do it. Today with smart phone apps and SMS, literally anyone can do it for free.That makes a lot of sense to me, seriously thanks for taking the time to explain it.
With MFA, not only does the hacker need to steal your password, they also need to steal your smartphone. Not likely for somebody sitting halfway across the world.
SMS codes are easier to intercept than rolling One Time Passcodes via a security app like Google Authenticator, but I'd still take a SMS code over nothing for somebody like us that doesnt have state secrets to protect.
Way off base here. PLCs are some of the most vulnerable systems. They may not have been connected to networks 30 years ago, but today they generally are. Welcome to IoT.PLC's in my opinion are pretty safe proves they aren't connected to the network and all firmware upgrades are thoroughly vetted.

Not only are PLCs connected, but their I/O devices are as well. More and more of these things are being connected all the time. Isolating them as much as possible is generally the only option. There are of course business driven issues with that. The first is the desire for access to systems for management/troubleshooting. Another problem is the desire to use analytics with the data that comes from them.
It is a constant battle between access and security.
Speaking of IoT. That has been one of the worst things to happen from a security perspective. More and more devices are put onto networks. Many/most of which have rudimentary security at best, and often never get updated to fix what issues are actually addressed by the manufacturers.
I think a typo caused a miscommunication. What I meant to say is they are safe "provided" they aren't connected to the network.Way off base here. PLCs are some of the most vulnerable systems. They may not have been connected to networks 30 years ago, but today they generally are. Welcome to IoT.
Not only are PLCs connected, but their I/O devices are as well. More and more of these things are being connected all the time. Isolating them as much as possible is generally the only option. There are of course business driven issues with that. The first is the desire for access to systems for management/troubleshooting. Another problem is the desire to use analytics with the data that comes from them.
It is a constant battle between access and security.
Speaking of IoT. That has been one of the worst things to happen from a security perspective. More and more devices are put onto networks. Many/most of which have rudimentary security at best, and often never get updated to fix what issues are actually addressed by the manufacturers.
Otherwise you are right iot has caused concerns in security. Hell a raspberry pi lead to a sec breach at NASA a few years ago.
Members online
- Indy574
- BeDome
- edwea
- DoggyDaddy
- Mgderf
- SEIndSAM
- Mongo59
- 10mm
- mo381
- Hoosierdood
- opus1776
- Okimeister
- cmann250
- red_zr24x4
- Magyars
- Nazgul
- tmschuller
- mike4sigs
- target64
- Dirty Steve
- COOPADUP
- jbm1521
- hammerd13
- x34822
- El Conquistador
- ranger04
- dboz
- Tomahawkman
- Lost Californian
- loudgroove
- NHT3
- AllenM
- cmamath13
- bub74
- fender
- jspy5
- williamsburg
- 92FSTech
- Grump01
- Steve
- snapping turtle
- littletommy
- jjohnson878
- Hassiebawked
- Aggar
- Simon6101
- slims2002
- PLANEMECH
- TacOpsGuy320
- Bybo
Total: 1,120 (members: 62, guests: 1,058)